Blog
In our blog posts and video formats, we explain everything you need to know about IT security – in easy-to-understand language.
Introducing: The Trufflepig Platform
16.03.2026

Hacker protection: This is how IT logins must be done in companies in 2025
15.11.2024

Phishing Awareness with Lucy Security: Strengthening Your Human Firewall
14.10.2024

Security Operations Center (SOC) for Businesses: What You Need to Know in an Emergency
11.06.2024

Risks posed by AI in IT security: a blessing or a curse for companies?
28.05.2024

Trufflepig expands into Switzerland with new location
24.04.2024

The 5 most common hacker attacks on companies in 2024
26.03.2024

Data theft by employees: How to prove it in your company
04.03.2024

Die 5 größten physischen IT-Sicherheitsrisiken im Unternehmen
26.02.2024

Danger from hacker attacks: What threatens your company in an emergency
23.02.2024
Avoiding common backup mistakes in IT security (video)
21.02.2024

2023 Year in Review & Outlook for 2024: How to protect your IT (video)
06.02.2024
After the risk analysis: Systematically securing IT against hacker attacks (video)
22.01.2024

Ransomware attack: How to effectively minimize damage in an emergency
11.01.2024

Training Employees Through Simulated Attacks: Building a True Human Firewall in 2026
10.01.2024
Ransomware 2026: Should You Pay? The High Cost of the "Quick Fix" and the Path to True Recovery
08.12.2023

Trufflepig supports AI-powered cybersecurity project (CAIDAN)
17.11.2023

How a small phishing email became a ransomware attack in an educational organization #case-report-1
08.11.2023
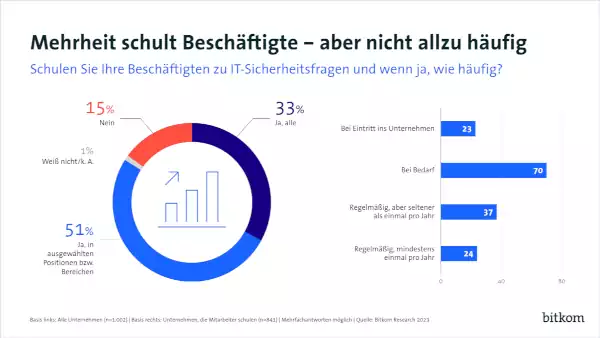
Bitkom study: Alarming need to catch up on IT training for employees
07.11.2023

Incident Response: What to do in the event of a hacker attack?
27.10.2023

What does a ransomware attack really cost? The financial consequences for companies
25.10.2023

Cyber insurance for businesses: What you need to know in an emergency (video)
20.10.2023
Avoid corporate liability in the event of hacker attacks
09.10.2023

Recognizing hacker attacks in your company and responding appropriately
18.09.2023
The 2026 Phishing Survival Guide: Clear Tips, AI Threats, and Actionable Defenses
13.09.2023

Successfully implement cyber risk analysis within a few weeks
25.08.2023
Ransomware 2026: Why Traditional Defense Fails and How to Build a Forensic-Grade Shield
18.08.2023

Cybersecurity in public service: Trufflepig pentest at KUS Pfaffenhofen
31.07.2023

IT forensics: What entrepreneurs need to know after an attack (video)
12.07.2023

How companies protect themselves from hacker attacks
11.07.2023
Valuable information on "IT security" once a month via Newsletter